The Twverify scam has been causing concern among social media users, particularly those with verified accounts.
Scammers are specifically targeting accounts with the coveted blue tick symbol, exploiting the trust and legitimacy associated with it. By hacking into these accounts or creating fake ones with blue ticks, scammers are able to deceive users and steal personal information and money.
In response, Meta, the parent company of Facebook, is actively working on advanced security features to combat this scam.
This article aims to uncover the fraudulent activities behind the Twverify scam and provide safety tips to protect users.
Table of Contents
What Is the Twverify Scam?
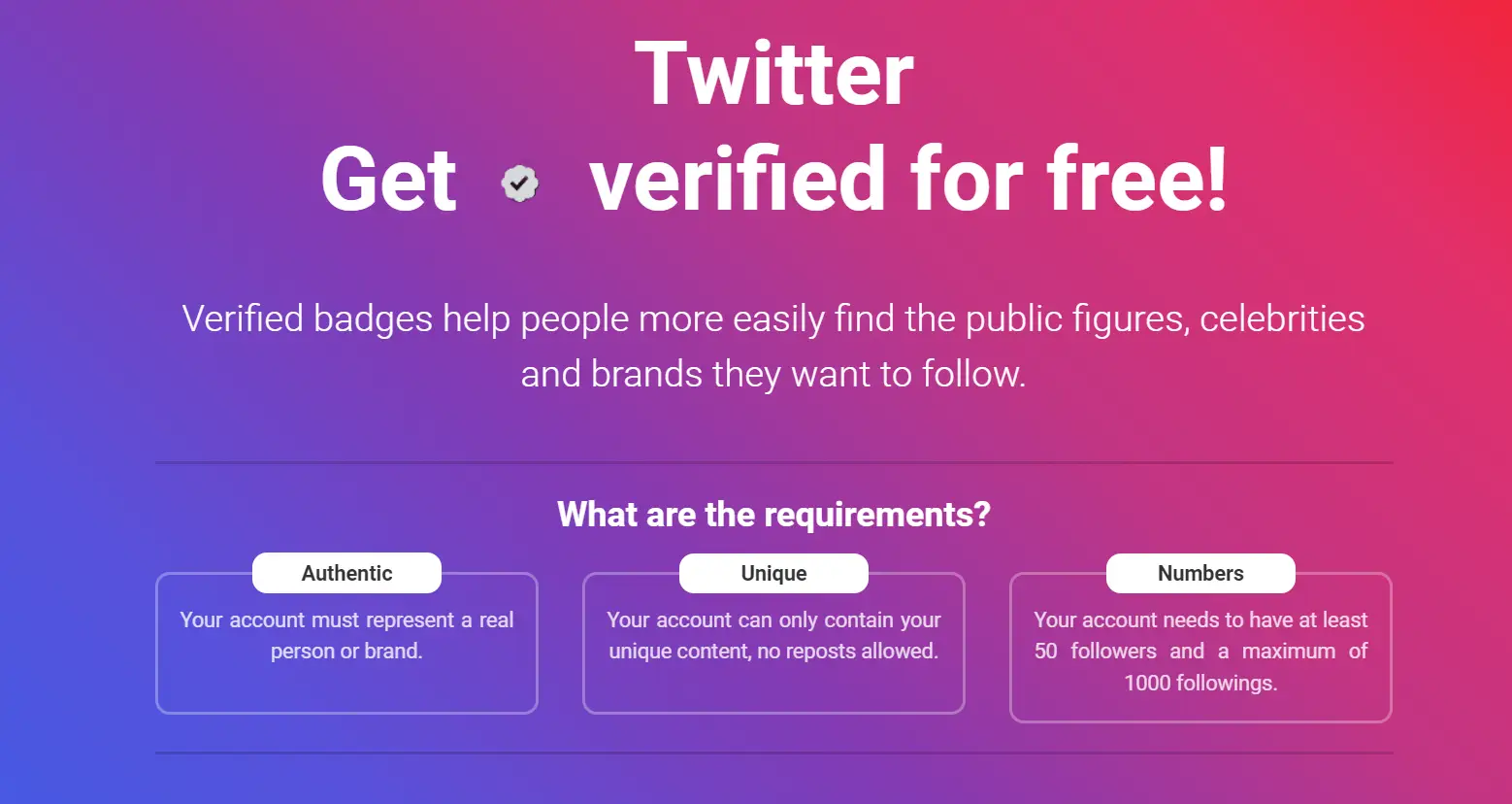
The Twverify scam is a fraudulent scheme where scammers hack verified accounts and exploit the blue tick symbol to deceive users and steal personal information.
How does this scam impact individuals? With the blue tick symbol signifying authenticity, scammers can easily trick users into thinking they are interacting with a genuine account. This can lead to users unknowingly sharing important information or falling victim to financial scams.
What prevention measures are in place? Meta, the parent company of Facebook, has disclosed this scam and is actively working on advanced security features to eliminate it. However, the challenge lies in differentiating between real and fake accounts, as scammers create fake profiles with blue ticks.
How can users protect themselves? It is crucial to be cautious while interacting with verified accounts and to stay informed about the latest safety tips provided by social media platforms.
How Does the Twverify Scam Works? – Techniques and Tactics
Hackers exploit verified accounts and deceive users by sharing links that lead to identity theft and financial loss. The impact on social media influencers is significant, as their verified accounts are seen as trustworthy and influential. This makes them prime targets for scammers who aim to deceive users and gain access to their personal information.
But how does the Twverify scam specifically target social media influencers and what role does social engineering play in it? The Twverify scam relies on social engineering tactics to manipulate users into clicking on deceptive links. By creating fake accounts with blue ticks and changing usernames, scammers trick users into thinking they are interacting with legitimate influencers.
This highlights the importance of awareness and caution among social media influencers to protect themselves and their followers from falling victim to this scam.
Red Flags and Warning Signs
Social media users should be wary of certain red flags and warning signs that may indicate they are being targeted by the Twverify scam. How can users identify these scams and protect themselves from falling victim? Here are three key indicators to watch out for:
Unusual requests for personal information: Scammers often pose as verified accounts and ask for sensitive data like passwords or financial details. Be cautious if you receive such requests, as legitimate accounts would not typically ask for this information.
Suspicious links or attachments: Scammers may share links on verified accounts that lead to phishing websites or malware-infected downloads. Exercise caution when clicking on any unfamiliar links or downloading attachments from untrusted sources.
Inconsistent account activity: Scammers frequently change usernames and create fake accounts with blue ticks to deceive users. If you notice sudden changes in an account’s profile information or a surge in suspicious activity, it could be a sign of a scam.
Customer Reviews and Experiences With the Twverify Scam
Users have shared their personal experiences and reviews regarding their encounters with the Twverify scam. It is evident that the impact on social media influencers has been significant. Many influencers have fallen victim to this scam, resulting in the loss of their verified accounts and the trust of their followers.
The scammers behind Twverify often target popular influencers with a large following, making it easier for them to trick users into sharing personal information or clicking on malicious links.
In response to this scam, legal actions have been taken against Twverify scammers. Law enforcement agencies and social media platforms are actively working together to identify and prosecute those responsible for these fraudulent activities. However, it remains a challenge to completely eradicate this scam due to the ever-evolving tactics employed by scammers.
It is crucial for users to remain vigilant and report any suspicious activity to prevent further harm.
How to Protect Yourself From Twverify Scam? – Safety Measures
Law enforcement agencies and social media platforms have implemented various security measures to combat the Twverify scam and protect individuals from falling victim to fraudulent activities. But what steps can individuals take to protect themselves from this scam?
Two factors that play a crucial role in safeguarding against such scams are the importance of Two Factor Authentication (2FA) and educating users on phishing awareness.
Importance of Two Factor Authentication: – Enable 2FA on all social media accounts to add an extra layer of security. – 2FA requires users to provide a second piece of evidence, such as a unique code sent to their mobile device, before gaining access to their accounts. – This helps prevent unauthorized access even if scammers manage to obtain login credentials.
Educating Users on Phishing Awareness: – Teach users how to identify phishing attempts, such as suspicious emails or messages requesting personal information. – Encourage users to verify the legitimacy of links before clicking on them. – Remind users to be cautious when sharing personal information online.
Conclusion
By implementing security measures and educating individuals, the Twverify scam can be effectively prevented. This will ensure a safer online environment for all.
The impact of the Twverify scam on social media platforms is significant. It undermines the trust and authenticity of verified accounts. Scammers exploit the blue tick symbol, deceiving users and stealing personal information.
To combat this, legal actions against scammers should be taken. This will hold them accountable for their fraudulent activities.
Platforms like Meta, the parent company of Facebook, are actively working to prevent such scams. They are developing advanced security features.
However, it is crucial for users to be aware of the risks and follow safety tips to protect themselves. By staying vigilant and reporting any suspicious activity, we can create a safer online space and ensure freedom from scams.
Frequently Asked Questions
Can the Twverify Scam Target Accounts Without the Blue Tick Verification?
Yes, accounts without the blue tick verification can be targeted by the Twverify scam. Scammers use impersonation techniques to deceive users and exploit their trust, regardless of whether they have the verification badge.
Are There Any Specific Social Media Platforms That Are More Vulnerable to the Twverify Scam?
Are some social media platforms more vulnerable to the twverify scam? How does this scam impact user trust and platform credibility? What measures are social media platforms taking to combat this scam?
How Long Has the Twverify Scam Been Active and How Widespread Is It?
How long has the Twverify scam been active and how widespread is it? The duration and extent of the Twverify scam are currently unknown. Further investigation is needed to determine the scale and impact of this fraudulent activity.
Are There Any Legal Actions Being Taken Against the Scammers Involved in the Twverify Scam?
Legal consequences and impact on victims of the Twverify scam are a major concern. Are there any ongoing legal actions against the scammers involved? How have the victims been affected, and what measures are being taken to provide justice and support?
What Are Some Common Methods Scammers Use to Hack Passwords and Gain Access to Verified Accounts in the Twverify Scam?
Common password-hacking methods involve phishing attacks, brute force attacks, and social engineering. To protect yourself from password hacks, use strong and unique passwords, enable two-factor authentication, and be cautious of suspicious emails or websites.
Also Read
Is Joules UK Scam or Legit? – Uncover the Hidden Secrets!
Cath Kidston UK Outlet Clearance Online Store Scam
Aus Vehicle Check Scam or Legit? Don’t Be a Victim!
Also Read
Scoredit.Com Review – Is Scoredit a Scam or Legit?
Timall.Shop Scam Exposed – Don’t Be the Next Victim!
Is Lowesus.shop Scam or Legit? Lowesus.shop Review
Also Read
Is Chuperex Legit or Scam? Avoiding Crypto Scams
Is Breedbarley.com Scam or Legit? Avoid Being Scammed!
Is Home Title Lock Scam or Legit? Discover the Truth!
Also Read
Is Videowalca Scam or Legit? Videowalca.Com Review
Gotexer Scam Crypto Website! Don’t Fall for Their Tricks
AnyVan Postman Scam – Beware Of Fb Marketplace Scam!
Also Read
DVLA Scam Explained – Don’t Fall Victim to Fraudsters!
Arwop Fashion Reviews – Is Arwop Fashion Legit or a Scam?
Ciciful Clothing Reviews – Real Insights and Potential Concerns
Also Read
Musabela Shoes Reviews – Is Musabela Legit or a Scam?
Lerynne West Scam – Discover the Shocking New Lottery Scam!
Regatta Discount Scam Exposed – Don’t Be Fooled by Unbelievable Deals!
Also Read
Is Natwest My Rewards Legit or a Scam? NatWest Reward Review
Macquarie Leasing Class Action Scam Text Exposed!
Benoit Dageville – Discover the Untold Story of Benoit Dageville!
Also Read
Is ACN Phone Scam or Legit? Discover the Truth About ACN!
Ohio Electricity Litigation Email Scam – Don’t Fall Victim!
Meta Support Team Scam – Don’t Fall Victim to Their Sneaky Tactics!
Also Read
NatWest Scam Email Alert – Natwest Warns Customers
Is Lovely Plants Legit or a Scam? Lovely Plants Review
Laxzoax com Legit or a Scam? Unveiling the Dark Side!
Also Read
Is Coinvest Legit or Scam? Discover the truth About Coinvest!
Is Organix Farmacy Legit or a Scam? Organix Farmacy Reviews
Canovania Jewelry Reviews – Uncover Authenticity Concerns!
Also Read
Elogyy Clothing Reviews – Discover the Truth About Elogyy Clothing!
Lavetir Dress Reviews – Bridesmaid Dresses Real or Hype?
Proptmina Bra Reviews – Is Proptmina Bra Worth Trying?
Also Read
Untups.com Scam Exposed – Don’t Fall for This USPS Impersonator